University Project - Basic Malware Lab
Navigating the Complex World of Malware Analysis: A Personal Journey
Introduction
In a recent video, I jumped into the intricate world of Malware Analysis. This engaging project involved diving into the depths of cybersecurity, exploring the stages, challenges, and invaluable learnings that arose along the way. In this blog post, we’ll take you through the highlights of this project and provide insights into the fascinating realm of malware analysis.
The Three Phases of the Project
The project was structured into three distinct phases, each contributing to a comprehensive understanding of malware analysis.
- Learning the Tools and Environment (Phase 1)
The initial phase revolved around familiarizing oneself with the necessary tools and setting up the ideal environment for malware analysis. This foundational step is crucial, as a strong understanding of the tools and systems is essential for accurate analysis.
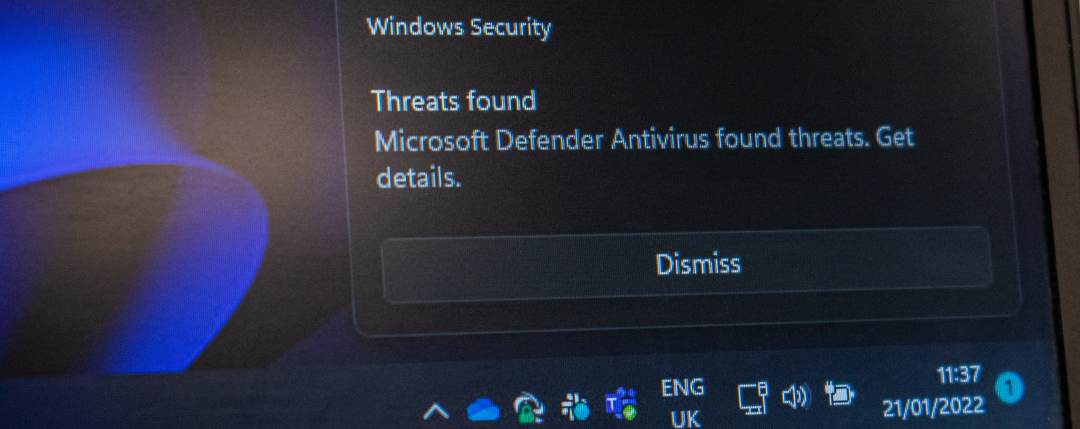
- Analyzing Malware (Phase 2)
The heart of the project involved delving into the actual analysis of malware. However, the journey wasn’t without its obstacles. The scarcity of readily available malware samples, particularly script-based malware, posed an initial challenge. Script-based malware often proves more accessible for analysis compared to compiled executables.
- Documenting and Publishing (Phase 3)
Once the malware analysis was conducted, the final phase encompassed the documentation and publication of the analysis process. This phase is pivotal for sharing knowledge with the cybersecurity community and facilitating collaborative learning.
Challenges Faced
As with any substantial project, numerous challenges presented themselves throughout this malware analysis endeavor. Here are some of the key hurdles:
-
Resource Scarcity: A shortage of resources, especially in the form of readily available malware samples, made the project more challenging. This scarcity meant that I had to adapt and learn how to convert existing VMware OVA files into a hyper-v environment.
-
Tooling Complexity: Understanding the various tools used in malware analysis proved to be a significant challenge. The project required a deep dive into the intricacies of these tools, adding a layer of complexity to the process.
-
Assembly Language Knowledge: Perhaps the most significant roadblock faced was the need for a deep understanding of assembly language (ASM). When encountering malware that presented itself in x86 ASM, it required an extensive effort to comprehend and analyze effectively.
Achievements and Reflections
Despite the hurdles encountered, this malware analysis project was not without its notable achievements:
-
Embracing Failure: The project reinforced the idea that failure is a natural part of any engineering endeavor. What’s crucial is the ability to learn from these failures, turning them into valuable lessons for future projects.
-
Tool Proficiency: I was able to enhance their skills in hyper-v, scripting, and using a variety of tools for malware analysis, solidifying their expertise in these areas.
-
Diverse Toolset: One of the most significant takeaways from the project was the extensive array of tools available for malware analysis. Approximately 15 tools were explored, each offering unique capabilities in dissecting and understanding malware.
-
Personal Growth: Reflecting on the project as a whole, it became evident that it was a challenging yet incredibly rewarding journey. It allowed Ito step out of their comfort zone, gain a deeper understanding of cybersecurity, and ultimately thrive in this demanding field.
Conclusion
The malware analysis project undertaken in this video offered a glimpse into the intricate world of cybersecurity. It showcased the importance of perseverance, adaptability, and the willingness to learn from failures. As I successfully navigated through phases, overcame challenges, and embraced the complexity of malware analysis, it serves as an inspiring example of personal and professional growth.
For those interested in exploring the project further or delving into the world of malware analysis, the associated code is available on the my’s GitHub repository . However, it’s essential to remember that such knowledge should be used responsibly and ethically, as the project was strictly intended for educational and research purposes.
